Appearing as an expert for over 9 years, you know the author from

The Pocket Guide for Investigating
Ransomware and Network IntrusionsThis book was written to assist you in understanding the technical, logistical and legal processes involved with these investigations.
There are many goals and objectives covered in this book, which must be completed successfully to address the legal and technical aspects of the project. For example, there may be legal compliance issues if you find personally identifiable information (PII) on one or more computers that an intruder accessed. My hope is that this book serves as a guide to keep you and your team focused and organized, and help you successfully complete the mission.
Who should read this book?
Attorneys
As a law firm, it is essential that you safeguard clients’ data.
Network Technicians
Overcome challenges to secure all of your endpoints and mitigate cyber threats
IT Professionals
Learn how not to fall prey to cybercrime & digital extortionists.
Data Security Technicians
Keep yourself, and your organization, abreast of the latest cybercrime threats.
Network Architects
To protect your network from a ransomware attack, it's critical that you have a detailed plan.
Firewall Technicians
Learn best practices for configuring your firewall and network to give you the best protection possible.
About the author
John Lucich is the Founder & CEO of the Network Security Group, where he has assessed, designed, and managed mid to large-size networks for corporations, government agencies, and casinos nationwide, for more than 20 years. He is also a retired State Criminal Investigator from the Organized Crime Racketeering & Corruption Bureau of the New Jersey Attorney General’s Office, Division of Criminal Justice, where he was directly involved in conducting high-tech crime investigations and computer forensics since 1988.
Mr. Lucich served five years as an adjunct professor of computer science at Felician College, and is a nationally recognized expert, lecturer, and published author on network security and computer forensics. In the early-2000s, he served as the keynote speaker for Network Associates, RSA, and Protegrity, at more than 50 computer security seminars throughout the U.S. and Canada. He also taught a cyber-crimes course at the New Jersey Attorney General’s academy in Sea Girt, for more than a decade.
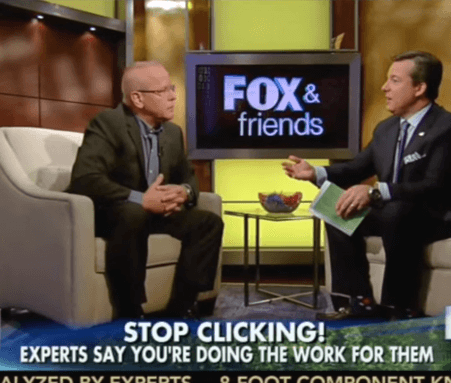
Mr. Lucich appeared as an expert on Fox News and CNN for nine years, speaking on topics of technology, network intrusions, and ransomware. He was a Keynote speaker with General Colin Powell and Bill Gates at CAWorld96, where he addressed computer security issues.
He has worked undercover for the US military and had identified individuals involved in military computer intrusions, and testified as an e-mail expert in the case of a New York State Judge who had lied about sending an e-mail to then-President Bill Clinton. He was also an expert witness against a New Jersey police officer, in a trial where the officer stood accused of taking a computer as a bribe. That officer was found guilty and removed from the force.
Mr. Lucich was the first state law enforcement officer to testify before the U.S. Congress in 1993 on computer crime issues. In February 1999, he testified as a high-tech crimes expert witness before the New Jersey State Commission of Investigation, as part of the state hearings on computer crimes in Trenton. In 2016, Mr. Lucich and his staff investigated a network intrusion and identified the hacker, a Chinese national, who was later indicted by federal prosecutors. A subsequent civil trial awarded the victim company more than $7 million in damages.